POODLE – CVE-2014-3566 – SSLv3 –What is it? and how to fix it?
On October 14 a new vulnerability in SSLv3 has been discovered. SSLv3 is an old protocol 18 years old which for the time of writing supported by all the browsers.
In fact, today when browsing a protected website (https) our browser uses SSL. The browser asks the server to with an SSL that is supported by sides, the user and the server. For example, The browser asks the server, do you support SSLv2, if it does a SSL communication starts between both sides, otherwise both sides will try to work with a different version, usually an older one.
Who is affected by POODLE?
The attack is considered as MITM (Man In The Middle) or in other words, no one could break to your computer by simply exploit this vulnerability, however this attack can be used in a way that can affect you. In fact this attack provides the attacker that is located on the same network as you are to read the encrypted network between your browser and the server. For example, if you are browsing to Gmail, the attacker that is also using the same network as you are, same LAN network might be able to extract your private emails and even your password to Gmail account, so in other words this attack still counts as critical.
Let’s take a real life scenario. Let’s say you are sitting in an internet café, connecting your laptop to the free WIFI and browsing to Facebook, or to your bank account. At this moment the attacker that is connected to the same free WIFI might be able to steal your personal information as long with your passwords.
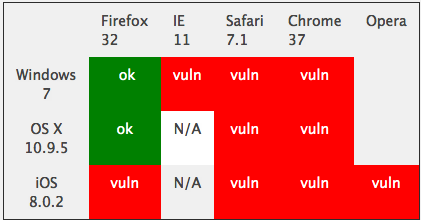
Following is a screenshot presents which browsers are prone to this vulnerability at the time the attack was discovered.
Taken from dhield.org
How to handle this (Server perspective)?
As a web server owner, we highly encourage you to disable SSLv3, since even though you will update SSL to the latest version, the user can be vulnerable to the attack in case his browser is not fully patched.
The problem of turning off SSLv3 is affecting the user experience, in fact it will prevent from specific users accessing the website in case their browser using only SSLv3.
The second option, which is less preferred is simply update SSL version, they latest version of the application fix the bug and prevent from the attacker to require the browser to use an older SSL version even though it has a newer one.
In order to update SSL version ins CentOS
yum –y update openssl
In order to disable SSLv3 in Apache, you should add the following line to the httpd configuration files
SSLProtocol All -SSLv2 -SSLv3
How to fix it (user’s perceptive)?
You can check by the link below whether your browser is vulnerable to this exploit
In case your browser is vulnerable you should disable SSLv3
Mozilla Firefox browser
In the URL write: about:config
Look for tls
Change the value of security.tls.version.min from 0 to 1 (TLS 1.0 = 1, SSL 3.0 = 0)
Chrome browser
You should start Google Chrome not by the regular icon, but the user the command line with:
Chrome –ssl-version-min=tls1
Internet Explorer browser
You should press on Settings, afterwards click on Internet Options and then press on Advanced
Remove the “checked” mark on the SSLv3 under the Security category.